What is Web Application Firewall (WAF)?
Web Application Firewall is one of the most common firewall types that serves specifically for web applications. In most cases, it effectively blocks out malicious actions from external parties such as hackers. Besides, it also analyses based on the HTTP traffic from and to the website application. Web Application Firewall could be implemented in both software and hardware, allowing it to provide greater protection to web applications by detecting and excluding possible vulnerabilities that lead to external threats.
What is Managed Firewall?
The setup and maintenance of Web Application Firewall is never easy, that’s when you need a managed firewall.Managed firewall is a combination of security threats assessment and network traffic monitoring. Normally speaking, a managed firewall solution will offer all-in-one set-up, operation, maintenance and optimization of Web Application Firewall rules. Some managed firewall solutions also provide clients with detailed analysis and follow-up reports.
After the security incident, a managed firewall will re-evaluate the system and conduct data recovery if necessary. Also, the managed firewall will learn from the previous inadequacies and update the Web Application Firewall to maximize the security. Internet attacks have evolved considerably, with criminals who monetize their illegal activities and adopt sophisticated methods. Web attacks are the most significant threats faced by organizations vulnerable to such approaches as cross-site scripting (XSS), SQL injection (SQLi), and cross-site request forgery (CSRF), all of which have become standard attacks. Partner with the trusted firewall service providers that specialized in Web Application Firewalls can safeguard your web applications and web servers.
Firewall Types: WAF VS IPS VS NGFW
Apart from the mentioned web application firewall, there are two types of firewalls that are also popular among businesses and individuals: Intrusion Prevention System and Next Generation Firewall. While web application firewalls would decide whether network traffic is suspicious or normal and then determine to block or allow it based on the application layers, Intrusion Prevention System is more likely to be used to avoid communications without authorization.
Next-Generation Firewall, on the other hand, provides additional security not only by inspecting in and out network traffic streams, but also would integrate intrusion to prevent and detect more threats such as sandboxing. There is a common misconception that we should only select one option from the firewall choices. The fact is, it is also possible to implement more than one firewall solution to have a higher level of security.
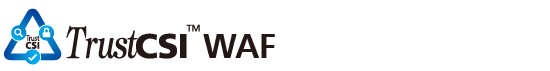
TrustCSI™ WAF - Effective Approach to Block Cyber Attacks
TrustCSI™ WAF could effectively prevent users from cyber threats in three main ways. Web application firewalls could detect and react to web application attacks very quickly. Online resources of the web application could be protected dynamically. It is also easy for the web application to adapt to different environments as there are only a few changes needed to be implemented. Combining the outstanding ability of web application firewalls to detect and stop malicious network traffic and the quick response from the security expert, real-time monitoring and security event management could run smoothly, which helps businesses to effectively block cyberattacks with fewer efforts.
Now feel secure with the confidence that your Website will always be available and responsive. Enjoy the versatility and freedom of continuous assistance and policy tuning from one of the managed firewall service providers, CITIC Telecom CPC. Its dedicated team of industry-certified Security Operations Center (SOCs) engineers who work round-the-clock to protect your applications and intellectual property, non-stop. TrustCSI™ WAF Managed Web Application Firewall service also features proactive security event management and response, real-time monitoring, specialized policies, attack reports, and 24x7 support. It is designed to be the most effective, most dependable, least cumbersome, and best value managed firewall service in the market.
Internet attacks have evolved considerably, with criminals who monetize their illegal activities and adopt sophisticated methods. Web attacks are the most significant threats faced by organizations vulnerable to such approaches as cross-site scripting (XSS), SQL injection (SQLi), and cross-site request forgery (CSRF), all of which have become standard attacks. Partner with the trusted firewall service providers that specialized in Web Application Firewalls can safeguard your web applications and web servers.
Now feel secure with the confidence that your Website will always be available and responsive. Enjoy the versatility and freedom of continuous assistance and policy tuning from one of the managed firewall service providers, CITIC Telecom CPC. Its dedicated team of industry-certified Security Operations Center (SOCs) engineers who work round-the-clock to protect your applications and intellectual property, non-stop. TrustCSI™ WAF Managed Web Application Firewall service also features proactive security event management and response, real-time monitoring, specialized policies, attack reports, and 24x7 support. It is designed to be the most effective, most dependable, least cumbersome, and best value managed firewall service in the market.